In today’s highly digitized world, we can no longer go more than a week without hearing news about high-profile data leak or massive cybercrimes. While many tech companies are doing their best to protect their customers’ private information, cybercriminals are always lurking in the digital shadows, trying to hatch new, sneaky workarounds. One such example is billing schemes.
As the name implies, a billing scheme is a malicious tactic where the creators of fraud either submits a false invoice or alters a valid one. The purpose is to trick the buyer into making a payment that should not be made. The buyer will receive what looks to be a legitimate invoice detailing services or goods that would be the type that’s usually purchased. However, this invoice is bogus that’s sent by a dummy company.
Billing schemes are rampant in the digital space. Many hackers and cybercriminals are continually developing malicious software. The purpose of this is to try to fool online consumers to steal them money or acquire their private information. That’s why you need to know how to protect yourself and your business from billing schemes.
There are many protective measures to be taken against fraud schemes and other online fraud. Most people think that they will never be scammed – until they are. This mindset is what online fraud criminals are exploiting. That’s why, as a responsible consumer or business owner, you must establish an online security measure to protect yourself from these heinous activities.
Table of Contents
Toggle1. Watch Out for Impostors
If you receive payment instructions via email or any other messaging platform from an unknown company, be sure to follow up with them or a trusted contact by phone. That way, you can verify if these instructions are legitimate. The same goes if you receive bank account updates to bank from a vendor. Never rely on messaging alone, as it may have been tampered with and compromised. It’s always essential to verify and confirm if this invoice true or not. Also, look for proof of this purchase and don’t just pay right away.
When updating the bank account for a particular vendor within your ReliaBills account, a message is shown reminding you to verify the authenticity of the bank account number. In addition, we also ask you to confirm if the details in the message are accurate and that you did make such a transaction with that company.
2. Use Bill Approval Workflows
The next thing you need to do is to use bill-approved workflows. That way, your employees, specifically the people who manage the billing department, will have a standard process of receiving and sending payment. Establish a standard bill approval policy and procedure. Specify when two or more employees must review and approve each bill before scheduling an amount. The trusted team members involved will add another layer of scrutiny and ensure that all payments are legitimate.
3. Require Images for All Payments
To reinforce the bill approval workflow that you will establish, make sure you submit bill images as well. That way, they can be reviewed by approvers and payers for authenticity and accuracy. So when someone purchases a service or product from you, make sure you send them images of the product so that you can ensure that your invoice will be legitimate and not be suspected as a fraud. At the same time; if you’re the buyer, make sure you request images of the product or service that you’re purchasing, as well as the vendor invoice for payment.
4. Invite Vendors to Join the ReliaBills Invoicing Network
One of the reasons why fraud exists is that there are multiple networks around the internet that vendors use to bill their clients. That’s why if you’re constantly purchasing product from a dedicated supplier, make sure you invite them to a single payment network. With ReliaBills, you can send and receive payment under a safe and secure system.
By inviting your vendors to our invoicing network, you can safely and securely update your payment information on their own. At the same time, you and your vendors can also create personalized invoices and purchase orders. You can also schedule them whenever a payment date is looming. On top of being a secure and effective invoicing system, one of the best features that ReliaBills offers is that it’s 100% FREE to use.
5. Set-up a Recurring Billing Strategy
One of the best ways to protect your business from billing schemes is to transition to a modern, automated billing strategy. Recurring billing is currently at the top as one of the most effective payment processing systems that can help improve your earning potential while protecting your business from fraud and cybercriminals.
What is Recurring Billing?
Recurring billing is a payment model that lets your business charge its customers continuously at predefined periods (weekly, bi-weekly, monthly, quarterly, annually, or at custom intervals) as payment for the products or services they buy. It is an everyday staple in the subscription industry.
When a customer subscribes to your product or service, having a recurring billing system will prompt them to provide their payment details and agree to allow your business to automatically deduct the proper amount from their account according to the predefined payment terms.
Is Recurring Billing Ideal for Your Business?
Recurring billing is an excellent billing strategy for any kind of business. However, it works very well if your business offers its products or services recurring (ongoing). Some notable examples of business models that benefit significantly from recurring billing are:
- Subscription businesses (Newspapers, magazines, SaaS, etc.)
- Business that requires memberships (Gyms, clubs, spa centers, etc.)
- Businesses that provide metered (usage-based) billing (Utility, internet, cable, etc.)
Why Recurring Billing?
Recurring billing is a payment strategy that offers a ton of benefits. However, to protect your business from billing schemes, we’ll narrow it down to two:
Maximum Security
The digital world is full of frauds, scams, and cybercriminals that are waiting to pounce on you and your business at any given notice. If you’re accepting payments online and you don’t have a safe and secure system, you will end up losing more money than you can earn due to various billing schemes.
Fortunately, you can negate all of these negativities when you incorporate a recurring billing strategy into your business. Recurring billing offers payment security, which is crucial in every business that accepts digital payment. It can also protect your customers’ payment information from digital fraud.
ReliaBills, for instance, and its recurring billing system implements strong PCI compliance while following secure sensitive data practices in accordance with strict industry standards. It also uses fraud detection and prevention tools that will help pinpoint problematic accounts.
Resolve Payment Failures
It’s not always about billing schemes. Sometimes, the issue is as simple as a payment failure. However, the implications of that failed payment can be significant enough to hinder your business’s earning potential. That’s why it still needs to be dealt with in the most effective and efficient way possible.
Payment failures are a common occurrence even with a recurring billing system already in place. It may be due to card errors like insufficient funds, card expiration, or incorrect card data. As you can see, these mistakes can be corrected. With recurring billing, you can do so while making it simpler and more convenient for you.
Instead of manually reaching out to a customer for a failed payment, the system will automatically notify the customer about their failed payment and the reason for it. That way, they can resolve it themselves by making the necessary course of action. Some recurring billing software like ReliaBills will even try to re-attempt the payment process to see if the issue is not on the system itself.
Recurring billing is an essential billing strategy that you should try for your business.
How to Create a New Recurring Invoice Using ReliaBills
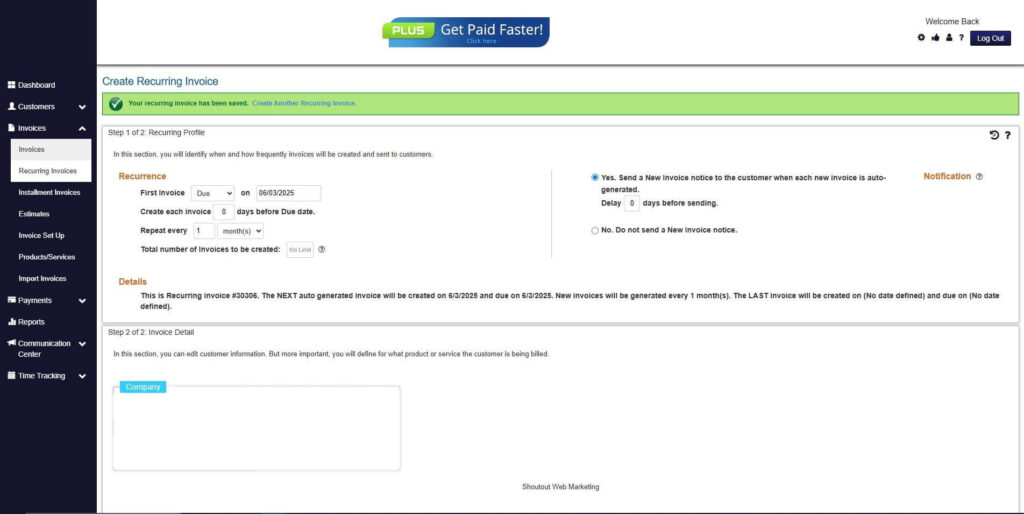
Creating a New Recurring Invoice using ReliaBills involves the following steps:
Step 1: Login to ReliaBills
- Access your ReliaBills Account using your login credentials. If you don’t have an account, sign up here.
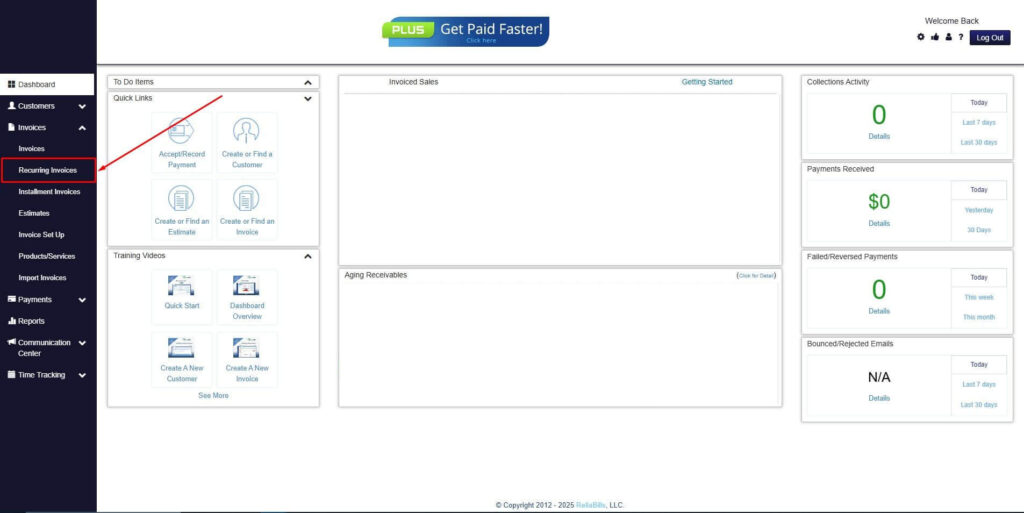
Step 2: Click on Recurring Invoices
- Navigate to the Invoices Dropdown and click on Recurring Invoices for an overview of the list of your existing customers.
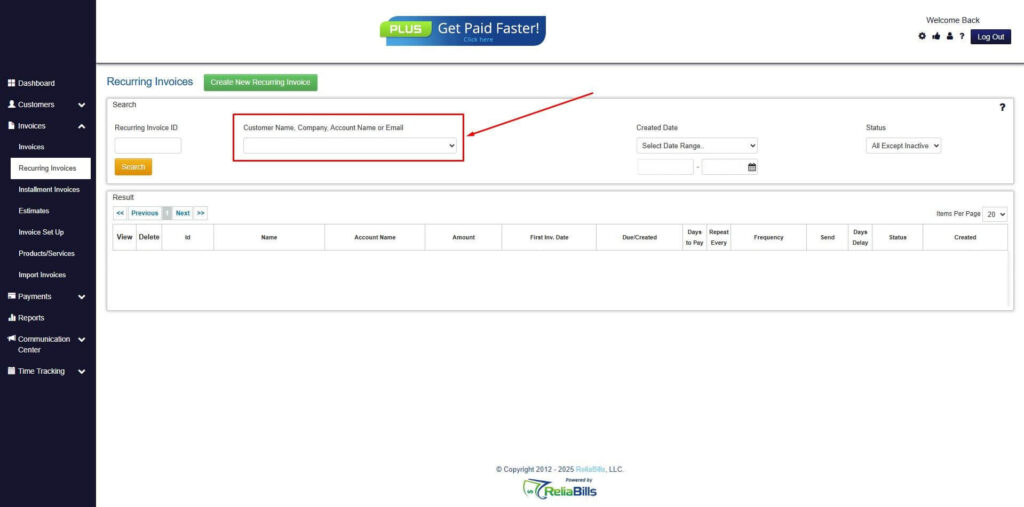
Step 3: Go to the Customers Tab
- If you have already created a customer, search for them in the Customers tab and make sure their status is “Active”.
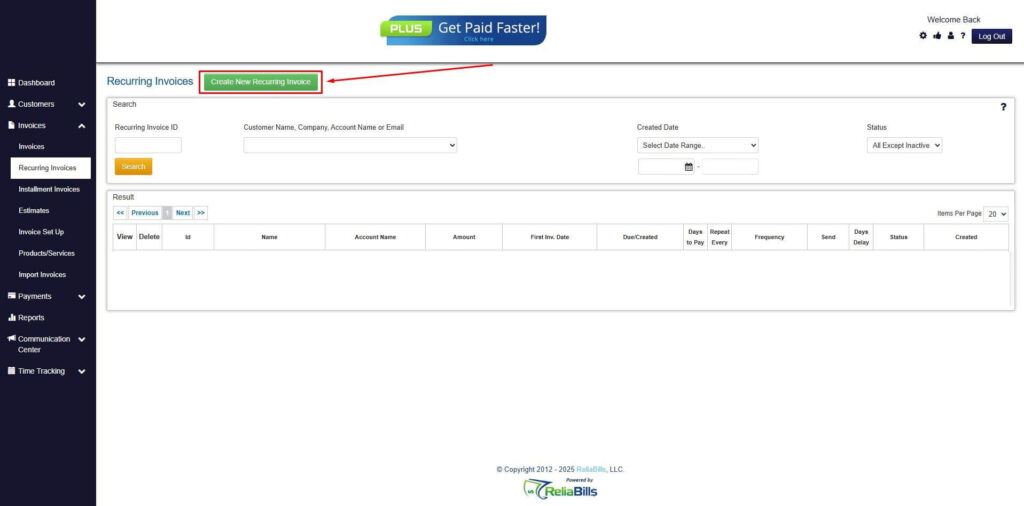
Step 4: Click the Create New Recurring Invoice
- If you haven’t created any customers yet, click the Create New Recurring Invoice to create a new customer.
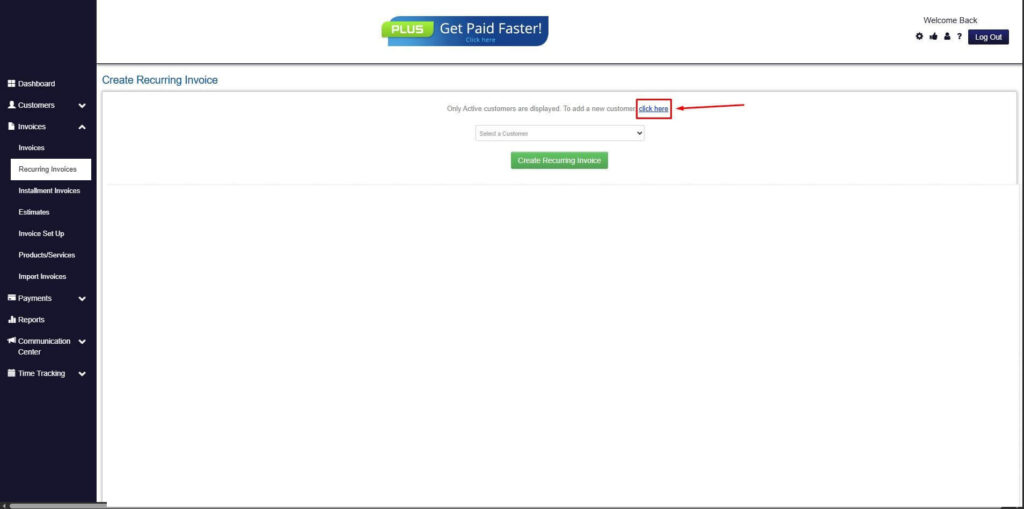
Step 5: Click on the “Click here” Button
- Click on the “Click here” button to proceed with the recurring invoice creation.
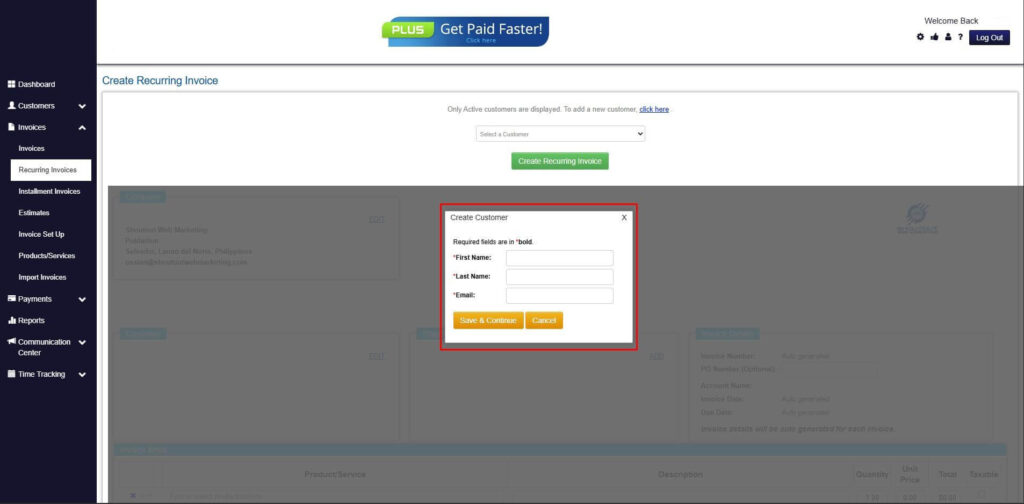
Step 6: Create Customer
- Provide your First Name, Last Name, and Email to proceed.
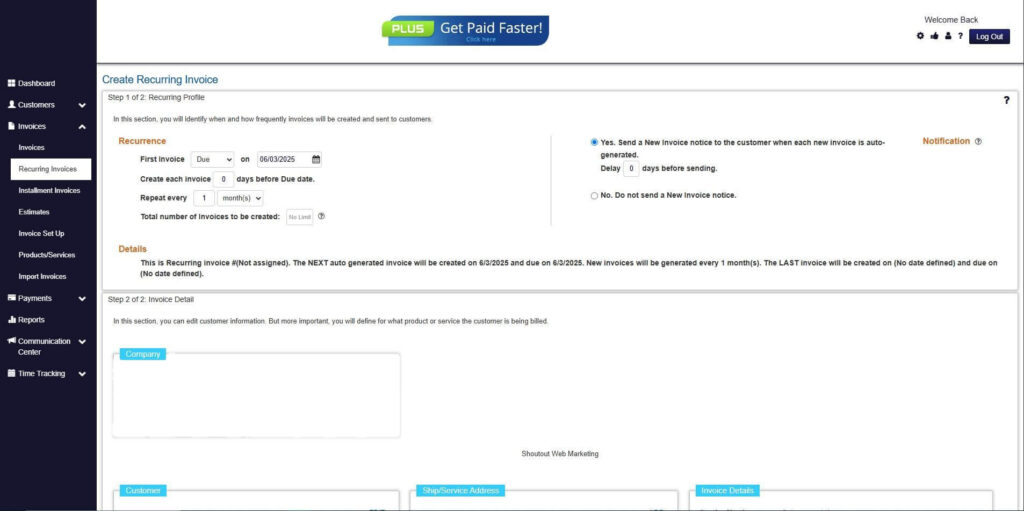
Step 7: Fill in the Create Recurring Invoice Form
- Fill in all the necessary fields.
Step 8: Save Recurring Invoice
- After filling up the form, click “Save Recurring Invoice” to continue.
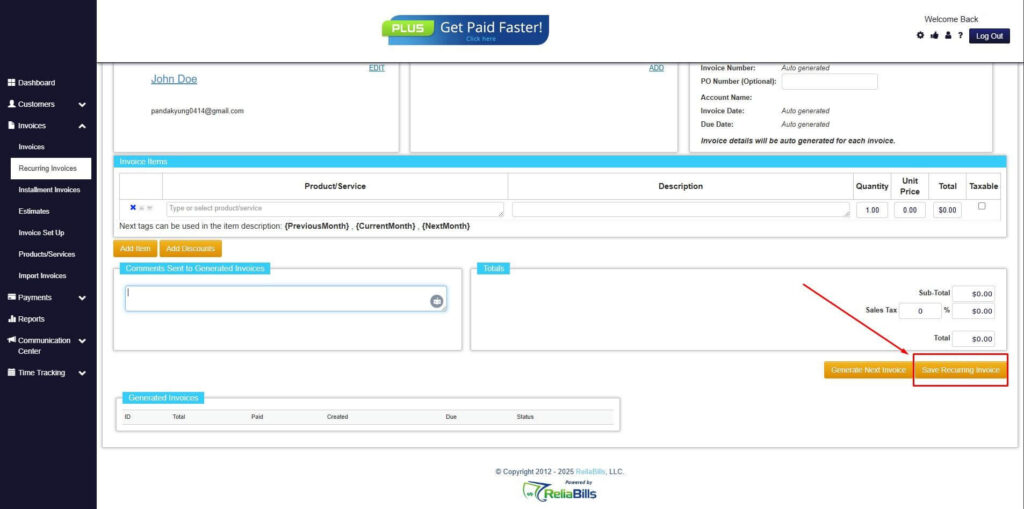
Step 9: Recurring Invoice Created
- Your Recurring Invoice has been created.
6. Watch Out for Unusual Payment Requests
Finally, you should watch out for any unusual payment requests that enter your inbox. Be extra vigilant with first-time vendors and international payments. In many cases, creators of online fraud have developed ways on how to acquire your personal details or trick you to make payment from them. Their systems have become so sophisticated that they can get information from you right away the moment you open their malicious emails. So make sure you know all of the transactions that you made online. That way, you can recall right away if you did make such purchases.
In addition, be wary of rushed or urgent payment requests. If you recall all of your payments and are updated with them all the time, you don’t have to rush anything. So, don’t cut corners to meet a deadline that may even be non-existent.
Other Cyber Security Tips to Prevent Fraud
Apart from these five tips that we mentioned, here are other best practices that you and your company should comply with to make sure you avoid falling for any billing scheme:
For Every Employee in the Company
- Watch out for bogus email messages disguised to appear official or real. It’s a common doing for fraudsters to spoof legitimate email domains with ones that look similar. For example, companyname@business.net or companyname@business.com instead of company name@business.com. As you can notice from the second example, the word, ‘business’ is lacking the letter’s.’ So if someone sends an email from a legitimate company yet their business email is lacking a letter, that’s a clear indication of a fraudulent and malicious email. That being said, you should also verify if the email is spelled right.
- Hover over or reply to an email address to make sure that it isn’t being masked as something that it’s not.
- Never let your guard down; be suspicious with everything. Only take action once you’re 100% sure that you’ve made purchase of that product and that you’ve verified the source of the email.
- Report and delete any unsolicited emails from unknown parties. Never open an email if it’s not familiar to you. Always verify first before you open anything that enters your inbox.
For the Management Staff in the Company
- Provide necessary training and advanced education for employees so that you can ensure that everyone in your company recognizes and is aware of billing or tampering schemes.
- Be careful of what you post on social media and other social platforms, especially job duties and descriptions, staff hierarchy, confidential information, and out-of-office details.
- Make sure that the employee or staff handling the billing department understands that cybercriminals may also pose as employees or vendors to try and manipulate them to do their bidding. So if you suspect that an employee email is not legitimate, report it or block it right away. That way, your bank statements are secure.
- Make sure you have a vendor list so that you will know which ones you communicate constantly and which ones are not. Details should include company name, vendor addresses, company funds, box address, shell companies (if any), and all rights reserved. The all rights reserved document should contain all the legal details of your transaction.
- Make sure you have an intrusion detection system in place. This system will flag emails with extensions that are similar to company emails. That way, you can avoid potential fraud.
Wrapping Up
By using all of the tips and advice that we’ve discussed in this article, you can protect yourself and your business from the risk of billing schemes. Always be mindful that these online phishing scams are everywhere on the internet. However, they can be prevented using these best practices.

